Dear experts,
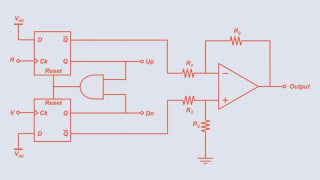
I want to learn how to write professional-quality code starting from my hobby projects. I’ve some components like an ATmega 8 MCU, EM-18 RFID reader, RTC DS1307, displays 16 *2 , relays, buzzer, red/green LEDs, push buttons, EEPROM, etc.
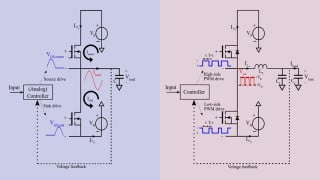
My idea is to combine these into a door access control system project. I can already program microcontrollers in C using Atmel Studio, and I’ve written some code before, but it’s mostly been in the “just get it working” style.
Now I’d like to learn how to structure things more like a professional embedded developer would splitting code into proper modules, writing drivers separately, organizing application logic, and following best practices.
I’m specifically looking for someone who can assist me here. point me in the right direction, review my approach, and help me understand how to do this step by step. I’m not asking for ready-made code. I want to learn the process and improve.
Any guidance, tips would be super appreciated.
I want to learn how to write professional-quality code starting from my hobby projects. I’ve some components like an ATmega 8 MCU, EM-18 RFID reader, RTC DS1307, displays 16 *2 , relays, buzzer, red/green LEDs, push buttons, EEPROM, etc.
My idea is to combine these into a door access control system project. I can already program microcontrollers in C using Atmel Studio, and I’ve written some code before, but it’s mostly been in the “just get it working” style.
Now I’d like to learn how to structure things more like a professional embedded developer would splitting code into proper modules, writing drivers separately, organizing application logic, and following best practices.
I’m specifically looking for someone who can assist me here. point me in the right direction, review my approach, and help me understand how to do this step by step. I’m not asking for ready-made code. I want to learn the process and improve.
Any guidance, tips would be super appreciated.

 Facebook
Facebook Google
Google GitHub
GitHub Linkedin
Linkedin